Cisco Asa Crypto Key Generate Rsa Asdm
To encrypt the SSH access you need to have an RSA keypair on the firewall, (Note: this is generated from the firewall’s host name, and its domain name, if you ever change either, the keypair will break, and SSH access will cease until the keypair is re-created). To create a key issue a “crypto key generate rsa” command. Because SSH uses RSA public keys to encrypt the sessions, you need to have consistent timing information. Example 3-16 shows not only how to manually adjust and verify timing information, but also how to create a domain name and generate RSA keys. Example 3-17 shows how to visualize SSH-related information in the Running-config. May 15, 2019 Also make sure you have generated an RSA key, had issues in the past: 'crypto key generate rsa modulus 2048' level 2 Original Poster 1 point 11 months ago edited 11 months ago. Generate CSR via Cisco ASA CLI Commands 1. Before generating a CSR request, you must create a private key (config)# crypto key generate rsa label itadminguide.key modulus 2048 INFO: The name for the keys. How about Cisco ASA? Today, I had to learn how to do it using CLI and not ASDM since I couldn’t find where the equivalent of aaa authentication ssh console LOCAL and crypto key gen rsa mod 4096 in the ASDM. Since I am really new to Cisco ASA, I am not well-versed in issuing commands under CLI. This article was created due to the COVID-19 pandemic.Customers are increasing AnyConnect licenses to allow a surge of AnyConnect sessions to their current headend ASA/Firepower.If using only existing hardware they are limited to the max.
KB ID 0000173
Problem
Quite a while ago I wrote the “Connecting to and managing Cisco firewalls” article, which is still pretty complete, but I’ve been asked on a few occasions, “How do I actually configure the firewall to allow remote administration via, SSH, or HTTPS/ASDM, or Telnet
If you have no network connection to the firewall, then you will need to connect via console cable (CLICK HERE).
Solution
Cisco ASA Allow SSH – Via Command Line
1. Log on to the firewall > Go to enable mode > Go to configure terminal mode.
2. Now you can either allow access for one machine, or a whole network, the syntax is “ssh {ip address} {subnet mask} {interface that you will be connecting to}.
3. You will need to create a username and password for SSH access, then set SSH to use the LOCAL database to check of usernames and passwords, (unless you are using LDAP, RADIUS, TACACS, or Kerberos for authentication.)
4. By default the SSH session times out after 5 mins, I prefer to change this to 45 minutes.
5. To encrypt the SSH access you need to have an RSA keypair on the firewall, (Note: this is generated from the firewall’s host name, and its domain name, if you ever change either, the keypair will break, and SSH access will cease until the keypair is re-created). To create a key issue a “crypto key generate rsa” command;
Note: I set the key size to 2048, this is considered good practice
7. Lastly, save the changes with a “write mem” command;
Cisco ASA Allow SSH – Via ASDM (version shown 6.4(7))
1. Connect via ASDM > Navigate to Configuration > Device Management > Management Access > ASDM/HTTPS/Telnet/SSH > Add > Select SSH > Supply the IP and subnet > OK. (Note you can set both the timeout, and the SSH versions you will accept, on this page also). Autocad 2012 licence key generator. Note you still need to generate the RSA Key (See step 5 above, good luck finding that in the ASDM – see the following article).
Cisco ASA – Enable AAA for SSH (Local Database) ASDM version 6.4(7)
Cisco ASA – Add a User to the Local Database
Cisco ASA – Allow HTTPS/ASDM – Via Command Line
1. Log on to the firewall > Go to enable mode > Go to configure terminal mode.
2. Now you can either allow access for one machine or a whole network, the syntax is “http {ip address} {subnet mask} {interface that it’s connected to}.
3. Unlike telnet and SSH, HTTPS/ADSM access is via the firewalls enable password (Unless you have enabled AAA logon). this password is set with the “enable password {password}” command. (Note: You will already have entered this password in step 1, only do this if you wish to change it).
4. You need to make sure that HTTPS access is enabled with a “http server enable” command.
5. Lastly, save the changes with a “write mem” command.
Cisco ASA – Allow HTTPS/ASDM – Via ASDM (version shown 6.4(7))
OK, the title of this might raise an eyebrow, but if you have access to the ASDM and you want to grant access to another IP/Network them you might want to do this. Connect via ASDM > Navigate to Configuration > Device Management > Management Access > ASDM/HTTPS/Telnet/SSH > Add > Select ASDM/HTTPS > Supply the IP and subnet > OK. (Note: You can also enable and disable the http Server here and change its port number).
Cisco ASA Allow Telnet – Via Command Line
WARNING: Telenet is insecure, if possible don’t use it, (usernames and password are sent unencrypted.)
1. Log on to the firewall > Go to enable mode > Go to configure terminal mode.
2. Now you can either allow access for one machine, or a whole network, the syntax is “telnet {ip address} {subnet mask} {interface that its connected to}.
Install Asdm Cisco Asa
3. To set the password you use the “passwd” command (yes that’s spelled correctly).
4. By default the telnet session times out after 5 mins, I prefer to change this to 45 minutes.
Cisco Asa Crypto Key Generate Rsa Asdm File
5. Lastly, save the changes with a “write mem” command.
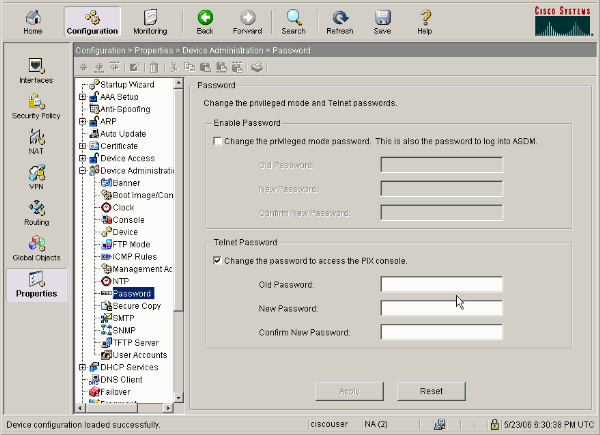
Allow Telnet – Via ASDM (version shown 6.4(7))
1. Connect via ASDM > Navigate to Configuration > Device Management > Management Access > ASDM/HTTPS/Telnet/SSH > Add > Select Telnet > Supply the IP and subnet > OK. (Note you can set the timeout on this page also). How do an hash key that generate less collution.
Related Articles, References, Credits, or External Links
Original Article Written 30/01/11