Generate Public Ssh Key On Mac
With a secure shell (SSH) key pair, you can create virtual machines (VMs) in Azure that use SSH keys for authentication, eliminating the need for passwords to sign in. This article shows you how to quickly generate and use an SSH public-private key file pair for Linux VMs. You can complete these steps with the Azure Cloud Shell, a macOS or Linux host, the Windows Subsystem for Linux, and other tools that support OpenSSH.
Generate Public Ssh Key On Mac Computer
Note
VMs created using SSH keys are by default configured with passwords disabled, which greatly increases the difficulty of brute-force guessing attacks.
- To generate a new key, tap the + button on the Keys pane of Prompt’s settings and choose Generate New Key. Choose a descriptive name for your key, and optionally set a passphrase. Choose your key type, and size. Then tap “Generate” to create your keypair. Once it’s finished generating, tap Copy Public Key to put the public key on your pasteboard. We’ll use it in the next step.
- In this quick tutorial, Generate SSH Key, we will learn more exactly how to generate a SSH Key in Linux or Mac using a terminal window and also in Windows using Putty. Before we start our little journey we should be clear about one thing, all SSH Keys consists of two parts, a Private Key and a Public Key.
Instead of using Amazon EC2 to create your key pair, you can create an RSA key pair using a third-party tool and then import the public key to Amazon EC2. For example, you can use ssh-keygen (a tool provided with the standard OpenSSH installation) to create a key pair. The standard OpenSSH suite of tools contains the ssh-keygen utility, which is used to generate key pairs. Run it on your local computer to generate a 2048-bit RSA key pair, which is fine for most uses. Ssh-keygen The utility prompts you to select a location for the keys. Mar 22, 2019 How to upload an SSH key via the DreamCompute dashboard; Connect to your DreamCompute Instance with SSH keys in Mac or Linux; How to configure passwordless login in Mac OS X and Linux; Creating and importing a Key pair using the OpenStack CLI; Creating a new Key. $ cd /.ssh $ ls authorizedkeys2 iddsa knownhosts config iddsa.pub You’re looking for a pair of files named something like iddsa or idrsa and a matching file with a.pub extension. The.pub file is your public key, and the other file is the corresponding private key. If you don’t have. With both Tectia SSH and OpenSSH servers, access to an account is granted by adding the public key to a /.ssh/authorizedkeys file on the server. To install the public key, Log into the server, edit the authorizedkeys file with your favorite editor, and cut-and-paste the public key output by the above command to the authorizedkeys file.
For more background and examples, see Detailed steps to create SSH key pairs.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Supported SSH key formats
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
Create an SSH key pair
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the ~/.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten.
The following command creates an SSH key pair using RSA encryption and a bit length of 4096:
If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the --generate-ssh-keys option. The key files are stored in the ~/.ssh directory unless specified otherwise with the --ssh-dest-key-path option. The --generate-ssh-keys option will not overwrite existing key files, instead returning an error. In the following command, replace VMname and RGname with your own values:
Provide an SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods:
If you're not familiar with the format of an SSH public key, you can display your public key with the following cat command, replacing ~/.ssh/id_rsa.pub with the path and filename of your own public key file if needed:
A typical public key value looks like this example:
Generate Ssh Key Windows
If you copy and paste the contents of the public key file to use in the Azure portal or a Resource Manager template, make sure you don't copy any trailing whitespace. To copy a public key in macOS, you can pipe the public key file to pbcopy. Similarly in Linux, you can pipe the public key file to programs such as xclip.
The public key that you place on your Linux VM in Azure is by default stored in ~/.ssh/id_rsa.pub, unless you specified a different location when you created the key pair. To use the Azure CLI 2.0 to create your VM with an existing public key, specify the value and optionally the location of this public key using the az vm create command with the --ssh-key-values option. In the following command, replace VMname, RGname, and keyFile with your own values:
If you want to use multiple SSH keys with your VM, you can enter them in a space-separated list, like this --ssh-key-values sshkey-desktop.pub sshkey-laptop.pub.
How To Generate Ssh Public Key In Mac
SSH into your VM
With the public key deployed on your Azure VM, and the private key on your local system, SSH into your VM using the IP address or DNS name of your VM. In the following command, replace azureuser and myvm.westus.cloudapp.azure.com with the administrator user name and the fully qualified domain name (or IP address):
If you specified a passphrase when you created your key pair, enter that passphrase when prompted during the login process. The VM is added to your ~/.ssh/known_hosts file, and you won't be asked to connect again until either the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.
Generate Public Ssh Key On Mac Os
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Next steps
For more information on working with SSH key pairs, see Detailed steps to create and manage SSH key pairs.
If you have difficulties with SSH connections to Azure VMs, see Troubleshoot SSH connections to an Azure Linux VM.
This guide goes through setting up SSH keys on macOS Mojave 10.14 back to Mac OSX 10.11 and also a secure password-less SSH connection between a local macOS workstation and a remote server also running a Linux variant operating system.
The process requires generating a public and private key on the local computer and then adding the public key to the remote servers authorised list. What is great about this is that it allows a password prompt free session, handy for a lot of uses.
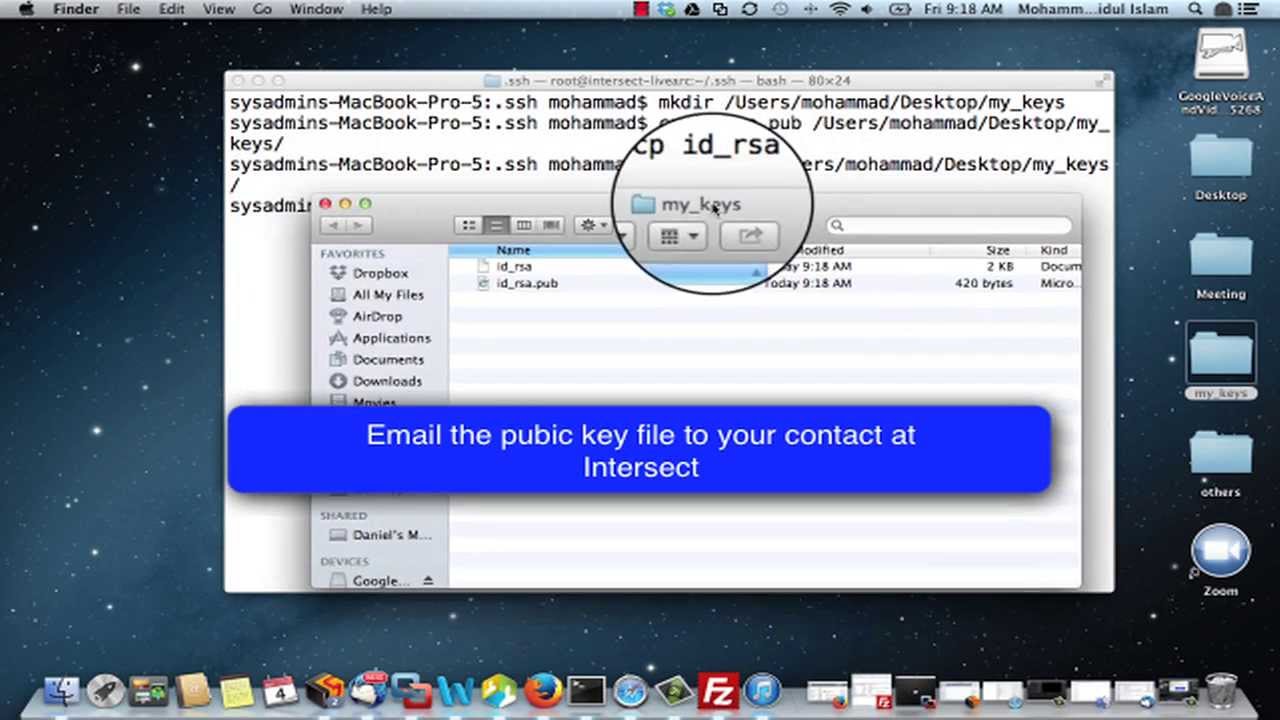
First thing that you need to do on your macOS machine is to create a directory that will store your SSH keys. Then you will generate a public and private key for your account, launch the Terminal and punch in some commands:
Mac Ssh Public Key
Create a .ssh Directory
Change to the home directory
Create a SSH directory name .ssh and move into it
Make sure that the file permissions are set to read/write/execute only for the user
Create your private and public key, the blank quotes at the end of the command gives the private key no password, so allowing for passwordless logins!
Change into the .ssh directory and list the contents of that .ssh directory
Thats your SSH keys created, the private key is the id_rsa and the public one is the id_rsa.pub, don’t give out the private one always keep that one only on your local machine.
Sharing the Public Key
Create an authorized_keys in the .ssh directory of the remote computer that you want to connect to.
You can create automatic logins by adding the contents of your public key to the authorized_keys file on the remote device.
To see and copy your public key use the cat command and copy the contents:
On the remote computer if needed, change the permssions on the authorized_keys file to write to add the public key, on a new line paste in your public key, and change permissions back to read only after for security.
Allow write on authorised_keys
Paste the entire id_rsa.pub content with vi or nano into the authorized_keys file, if using nano use the -w flag to not use incorrect line breaks.
If the remote host does not have an “authorized_keys” file simply create one and after the public key is pasted in don’t forget to takeaway write permissions.
Going Both Ways
So now when you connect via SSH no password is prompted as the remote computer has your public key which is only decrypted by your private key held in your local .ssh/ directory. If you want the communications to be bilateral then repeat the process in the opposite order between the two.
Now the two computers can securely connect with no password prompting, making it ideal to script between the two for file copies or back ups.
Doing it Quicker
Now instead of typing in
Make an alias in your bash shell you could alias it to
Reload the the shell
Then all you have to type in is the alias