Gpg Generate Key Without Passphrase
Use the gpg -list-secret-keys -keyid-format LONG command to list GPG keys for which you have both a public and private key. A private key is required for signing commits or tags. A private key is required for signing commits or tags.
- Generate Gpg Key Windows
- Gpg Generate Key Without Passphrase Key
- Gpg Generate Key Without Passphrase Download
In some cases you may need to generate and manage GPG keys on Ubuntu Linux servers or desktops… As you may already know, GPG encryption helps keep files save and secure… Origin key generator all games.
Using GPG encryption to encrypt your data before transfer ensures that they will not be viewed or read by anyone without a valid matching key pair… This technology works across diverse platforms, including Windows, Mac OS and Linux…
This brief tutorial shows students and new users how to generate and mange GPG keys on Ubuntu servers or desktops…
When you’re ready to get GPG working on Ubuntu, follow the steps below:
Feb 28, 2016 gpg-keygen. A readme and a script to generate PGP keys using GnuPG, using the current best practices. Its goal is to provide a concise and up-to-date description of best practices regarding the usage of GnuPG. A basic understanding of public key cryptography, and GnuPG in particular is assumed. Apr 29, 2013 Introduction This is how to create a gpg key without any user interaction or password. This can be used in cases where the primary goal is to secure the data in transit but the gpg key can/must be stored locally without a password. An example of this is.
Apr 04, 2017 gpg -import bobpublickey.gpg Conclusion. Now we have notions on the principles to use and generate a public key. You know how GnuPG is functioning and you can use it for secure communication. GPG encryption is only useful when both parties use good security practices and are vigilant. Read Also: How to Encrypt/Decrypt File using GPG in Linux. This option is a no-op for GnuPG 2.1 and later. See the previous subsection “Ephemeral home directories”.%ask-passphrase%no-ask-passphrase. This option is a no-op for GnuPG 2.1 and later.%no-protection. Using this option allows the creation of keys without any passphrase protection. This option is mainly intended for regression tests.%transient-key. To create a key, use the key generation wizard, which is started by running gpg.exe -gen-key. Enter the appropriate details whenever ask, but omit the password (by simply pressing the enter button; be aware no output does show up on the command line if typing passwords!). Generating a Keypair. To begin using GnuPG, you must first generate a new keypair: a public key and a private key. To generate a keypair, at a shell prompt, type the following command. Once you enter and verify your passphrase, your keys are generated, and a message similar to the following is displayed.
Step 1: Install GnuPG
In order to use GPG encryptions, you will have to install a software that helps generate and manage your GPG encryptions and keys… On Linux systems, a popular tool to help with GPG is GnuPG…
GnuPG is a free software implementation of the OpenPGP standard that allows you to encrypt and sign your data and communications using GPG encryptions.
On Ubuntu, open your command line terminal and run the commands below to install GnuPG…
After installing GnuPG, run the commands below to see if it’s installed and which encryption algorithms are supported… run the commands below:
Step 2: Generating Your GPG Key Pair
Now that GnuPG is installed, you’ll need to generate your own GPG key pair, consisting of a private and public key….
The private key is your master key… It allows you to decrypt/encrypt your files and create signatures which are signed with your private key…
The public key is shared with those who should open and view content you encrypt with your private key and also verifies that the content encrypted with your private key actually come you…
To generate your key pair, run the commands below:
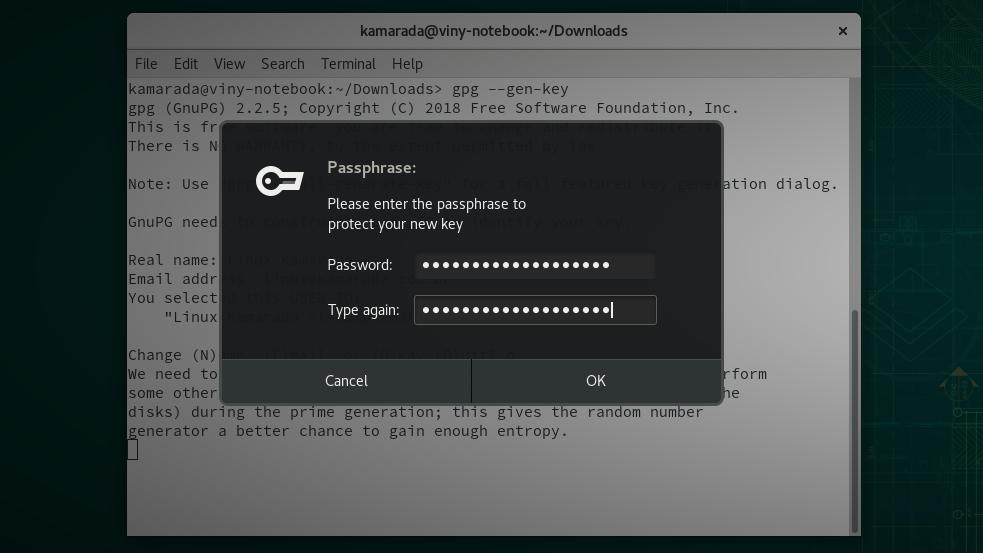
gpg –gen-key
That should initial GPG key generation process… You will be asked your real name and email address to use to identify the key… You should see similar output as below:
You’ll be prompted to type and confirm your passphrase for the private key…
After that, your keypair should be generated…
Exporting Your Public Key
If you need to export and share your public key to others, you run the commands below… The public key is used to authenticate that the content encrypted by you actually came from you…
It is also used to decrypt the content you encrypted…
gpg --armor --export admin@example.com > public_key.asc
You can also use the commands below to export the key into a readable text file…
gpg --armor --output key.txt --export admin@example.com
You can then send the public key file to those who should get it.
Encrypting and Decrypting Files
To encrypt a file you want to secure, you run the commands below… The public.text file becomes confidential.text.enc protected file.
gpg --encrypt --recipient 'admin@example.com' --output confidential.txt.enc public.txt
You should see an output as below:
You can now delete the public.txt file and only have the encrypted version…
Decrypting Files

To decrypt the confidential.txt.enc file using the public key… run the commands below:
gpg --decrypt --output public.txtconfidential.txt.enc
You’ll be asked to provide your passphrase to allow access to your private key to be able to decrypt the file…
Enter the key to decrypt…
The confidenatial.txt.enc file becomes public.txt.
That should do it!
For Windows users, they can use Gpg4win instead…
You may also like the post below:
| Key-Type: 1 |
| Key-Length: 2048 |
| Subkey-Type: 1 |
| Subkey-Length: 2048 |
| Name-Real: Root Superuser |
| Name-Email: root@handbook.westarete.com |
| Expire-Date: 0 |
| # Generate the key |
| gpg --batch --gen-key gen-key-script |
commented Feb 13, 2014
Here's a page that describes the options for the gen-key script: http://www.gnupg.org/documentation/manuals/gnupg-devel/Unattended-GPG-key-generation.html |
commented Feb 13, 2014
Originally I had a couple extra steps to use rng-tools to seed entropy from /dev/urandom. Apparently this is a bad idea because it will just feed bytes regardless of whether there's enough entropy. Here's where I got the original idea, and the subsequent discussion of why it's bad. For new machines, we should generate the keys on our laptops where there's much more entropy to draw from, and then transfer them to the new server, just like we're currently doing with the encrypted data bag secret. |
commented Feb 19, 2018
This is awesome, thank you. |
Generate Gpg Key Windows
commented Jan 23, 2019
I configured libvirt tu use /dev/urandom of the host: https://libvirt.org/formatdomain.html#elementsRng |
Gpg Generate Key Without Passphrase Key
commented Apr 9, 2019 • edited
edited
Gpg Generate Key Without Passphrase Download
Thanks that was really helpful |