Generates Two Different Yet Mathematically Related Keys
10.12.2020
public key algorithm
A cipher that manipulates an entire block of plaintext at one time. Blowfish A block cipher that operates on 64-bit blocks and can have a key length from 32 to 448 bits. A block cipher that processes blocks of 64 bits. A stream cipher that will accept keys up to 128 bits in length. Bitdefender total security 2016 key generator free download. A block cipher that can accept different length keys & blocks. A cipher that has three key sizes (128,192, and 256 bit) and performs 20 rounds on each block.
- خوارزمية المفتاح العموميAn asymmetric cipher that uses two keys, one for encryption, the public key, and the other for decryption, the private key. As implied by the key names, the public key used to encode plaintext can be made available to anyone. However, the private key must remain secret. Only the private key can decrypt the ciphertext. The public key algorithm used in this process is slow (on the order of 1,000 times slower than symmetric algorithms), and is typically used to encrypt session keys or digitally sign a message.
An asymmetric cipher that uses two keys, one for encryption, the public key, and the other for decryption, the private key. As implied by the key names, the public key used to encode plaintext can be made available to anyone. However, the private key must remain secret. Only the private key can decrypt the ciphertext. The public key algorithm used in this process is slow (on the order of 1,000 times slower than symmetric algorithms), and is typically used to encrypt session keys or digitally sign a message.
Automatic translation: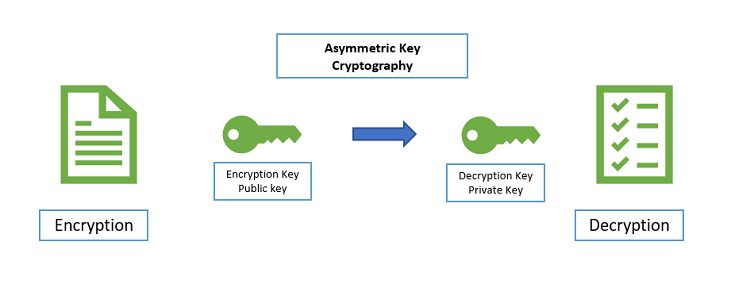
Generates Two Different Yet Mathematically Related Keys 2017
public key algorithm