Generate Security Audits Registry Key
- Advanced Audit Policy Registry Keys
- Penetration Testing
- Generate Security Audits Registry Key West
- Generate Security Audits Registry Key Windows 10
- Generate Security Audits Registry Key Software
- Jun 22, 2012 Added permissions to the registry key, but it didn’t help. The solution for me was to give the database engine service account permissions to the “Generate Security Audits” under User Rights Assignment in Local Security Policy. Thanks for post, Jeff T: @jlangdon.
- Enable the Security Auditing. For security auditing, it is required to either modify default domain policy or create a new Group Policy Object and edit it. You have to, in fact, deal with Advanced Audit Policy Configuration for this. Perform the following steps for enabling the security auditing of Active Directory in Windows Server 2012.
- Jun 24, 2016 Description; Inappropriate granting of user rights can provide system, administrative, and other high level capabilities. The 'Generate security audits' user right specifies users and processes that can generate Security Log audit records, which must only be the system service accounts defined.
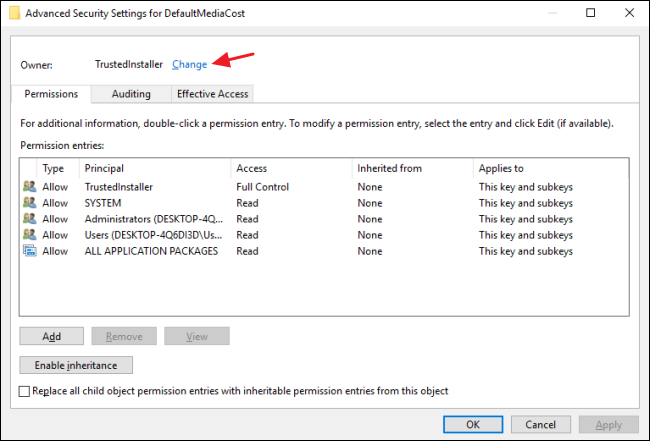
Enable Windows Logins for Local and Remote Audits. Qsr nvivo 10 key generator. The most important aspect about Windows credentials is that the account used to perform the checks should have privileges to access all required files and registry entries, which in many cases means administrative privileges. Mar 12, 2020 Enable Registry Access Audit Security (SACL) 1. Right-click on the Registry key which you want to configure audit events, and click Permissions. In Security window, click Advanced button. Navigate to the tab Auditing, and click Add button. Select the account Everyone, and check.
-->Applies to
- Windows 10
This reference for IT professionals provides information about the advanced audit policy settings that are available in Windows and the audit events that they generate.
The security audit policy settings under Security SettingsAdvanced Audit Policy Configuration can help your organization audit compliance with important business-related and security-related rules by tracking precisely defined activities, such as:
- A group administrator has modified settings or data on servers that contain finance information.
- An employee within a defined group has accessed an important file.
- The correct system access control list (SACL) is applied to every file and folder or registry key on a computer or file share as a verifiable safeguard against undetected access.
You can access these audit policy settings through the Local Security Policy snap-in (secpol.msc) on the local computer or by using Group Policy.
Advanced Audit Policy Registry Keys
These advanced audit policy settings allow you to select only the behaviors that you want to monitor. You can exclude audit results for behaviors that are of little or no concern to you, or behaviors that create an excessive number of log entries. In addition, because security audit policies can be applied by using domain Group Policy Objects, audit policy settings can be modified, tested, and deployed to selected users and groups with relative simplicity.Audit policy settings under Security SettingsAdvanced Audit Policy Configuration are available in the following categories:
Account Logon
Configuring policy settings in this category can help you document attempts to authenticate account data on a domain controller or on a local Security Accounts Manager (SAM). Unlike Logon and Logoff policy settings and events, which track attempts to access a particular computer, settings and events in this category focus on the account database that is used. This category includes the following subcategories:
Account Management
The security audit policy settings in this category can be used to monitor changes to user and computer accounts and groups. This category includes the following subcategories:
Detailed Tracking
Detailed Tracking security policy settings and audit events can be used to monitor the activities of individual applications and users on that computer, and to understand how a computer is being used. This category includes the following subcategories:
DS Access
DS Access security audit policy settings provide a detailed audit trail of attempts to access and modify objects in Active Directory Domain Services (AD DS). These audit events are logged only on domain controllers. This category includes the following subcategories:
Logon/Logoff
Logon/Logoff security policy settings and audit events allow you to track attempts to log on to a computer interactively or over a network. These events are particularly useful for tracking user activity and identifying potential attacks on network resources. This category includes the following subcategories:
Object Access
Object Access policy settings and audit events allow you to track attempts to access specific objects or types of objects on a network or computer. To audit attempts to access a file, directory, registry key, or any other object, you must enable the appropriate Object Access auditing subcategory for success and/or failure events. For example, the file system subcategory needs to be enabled to audit file operations, and the Registry subcategory needs to be enabled to audit registry accesses.
Proving that these audit policies are in effect to an external auditor is more difficult. There is no easy way to verify that the proper SACLs are set on all inherited objects. To address this issue, see Global Object Access Auditing.
This category includes the following subcategories:
Policy Change
Policy Change audit events allow you to track changes to important security policies on a local system or network. Because policies are typically established by administrators to help secure network resources, monitoring changes or attempts to change these policies can be an important aspect of security management for a network. This category includes the following subcategories:
Privilege Use
Permissions on a network are granted for users or computers to complete defined tasks. Privilege Use security policy settings and audit events allow you to track the use of certain permissions on one or more systems. This category includes the following subcategories:
System
Penetration Testing
System security policy settings and audit events allow you to track system-level changes to a computer that are not included in other categories and that have potential security implications. This category includes the following subcategories:
Global Object Access Auditing
Global Object Access Auditing policy settings allow administrators to define computer system access control lists (SACLs) per object type for the file system or for the registry. The specified SACL is then automatically applied to every object of that type.Auditors will be able to prove that every resource in the system is protected by an audit policy by viewing the contents of the Global Object Access Auditing policy settings. For example, if auditors see a policy setting called 'Track all changes made by group administrators,' they know that this policy is in effect.
Resource SACLs are also useful for diagnostic scenarios. For example, setting the Global Object Access Auditing policy to log all the activity for a specific user and enabling the policy to track 'Access denied' events for the file system or registry can help administrators quickly identify which object in a system is denying a user access.
Note: If a file or folder SACL and a Global Object Access Auditing policy setting (or a single registry setting SACL and a Global Object Access Auditing policy setting) are configured on a computer, the effective SACL is derived from combining the file or folder SACL and the Global ObjectAccess Auditing policy. This means that an audit event is generated if an activity matches the file or folder SACL or the Global Object Access Auditing policy.
This category includes the following subcategories:
-->Applies to
- Windows 10
Describes the best practices, location, values, policy management, and security considerations for the Generate security audits security policy setting.
Reference
This policy setting determines which accounts can be used by a process to generate audit records in the security event log. The Local Security Authority Subsystem Service (LSASS) writes events to the log. You can use the information in the security event log to trace unauthorized device access.
Constant: SeAuditPrivilege
Possible values
- User-defined list of accounts
- Local Service
- Network Service
Best practices
- Because the audit log can potentially be an attack vector if an account is compromised, ensure that only the Local Service and Network Service accounts have the Generate security audits user right assigned to them.
Location
Computer ConfigurationWindows SettingsSecurity SettingsLocal PoliciesUser Rights Assignment Eset smart security key generator.
Default values
By default, this setting is Local Service and Network Service on domain controllers and stand-alone servers.
The following table lists the actual and effective default policy values for the most recent supported versions of Windows. Default values are also listed on the policy’s property page.
| Server type or GPO | Default value |
|---|---|
| Default Domain Policy | Not defined |
| Default Domain Controller Policy | Local Service Network Service |
| Stand-Alone Server Default Settings | Local Service Network Service |
| Domain Controller Effective Default Settings | Local Service Network Service |
| Member Server Effective Default Settings | Local Service Network Service |
| Client Computer Effective Default Settings | Local Service Network Service |
Policy management
This section describes features, tools, and guidance to help you manage this policy.
A restart of the computer is not required for this policy setting to be effective.
Any change to the user rights assignment for an account becomes effective the next time the owner of the account logs on.
Generate Security Audits Registry Key West
Misuse of this user right can result in the generation of many auditing events, potentially hiding evidence of an attack or causing a denial-of-service (DoS) if the Audit: Shut down system immediately if unable to log security audits security policy setting is enabled.
Group Policy
Settings are applied in the following order through a Group Policy Object (GPO), which will overwrite settings on the local computer at the next Group Policy update:
- Local policy settings
- Site policy settings
- Domain policy settings
- OU policy settings
Generate Security Audits Registry Key Windows 10
When a local setting is greyed out, it indicates that a GPO currently controls that setting.
Security considerations
This section describes how an attacker might exploit a feature or its configuration, how to implement the countermeasure, and the possible negative consequences of countermeasure implementation.
Vulnerability
A malicious user could use accounts that can write to the Security log to fill that log with meaningless events. If the computer is configured to overwrite events as needed, malicious users could use this method to remove evidence of their unauthorized activities. If the computer is configured to shut down when it is unable to write to the Security log, and it is not configured to automatically back up the log files, this method could be used to create a DoS condition.
Countermeasure
Ensure that only the Local Service and Network Service accounts have the Generate security audits user right assigned to them.
Potential impact
None. Restricting the Generate security audits user right to the Local Service and Network Service accounts is the default configuration.