Generate Data Key From Kms
Dec 13, 2017 In envelope encryption we generate a data key by using our CMK at KMS. When generating the data key, AWS sends us both the plaintext key and the encrypted key (using our CMK). Then we use the. Aws kms enable-key: Enable-KMSKey: aws kms enable-key-rotation: Enable-KMSKeyRotation: aws kms encrypt: Invoke-KMSEncrypt: aws kms generate-data-key: New-KMSDataKey: aws kms generate-data-key-pair: New-KMSDataKeyPair: aws kms generate-data-key-pair-without-plaintext: New-KMSDataKeyPairWithoutPlaintext: aws kms generate-data-key-without. May 12, 2019 The Amazon S3 PutObject API needs code kms:GenerateDataKey/code when the bucket has default encryption enabled using a Customer Master Key. This is described in. The example program uses AWS KMS keys to encrypt and decrypt a file. A master key, also called a Customer Master Key or CMK, is created and used to generate a data key. The data key is then used to encrypt a disk file. The encrypted data key is stored within the encrypted file.
- Generate Data Key From Kms Free
- Generate Data Key From Kms Pdf
- Data Key Entry
- Generate Data Key From Kms To Meters
- Generate Data Key From Kms To Miles
AWS KMS then uses the specified CMK to generate data keys. As you can see from the below figure it generates one plaintext data key and an encrypted data key. This plaintext data key is used to encrypt the data, then the plaintext key is removed ASAP from the memory so that data doesn’t get compromised. Generates a data key that you can use in your application to locally encrypt data. Open AWS documentation Report issue Edit reference Supported Resource-Level Permissions. For more details on PCI DSS compliant services in AWS, you can read the PCI DSS FAQs. Q: How does AWS KMS secure the data keys I export and use in my application? You can request that AWS KMS generate data keys and return them for use in your own application. The data keys are encrypted under a master key you define in AWS KMS so that you can.
Q: What is AWS Key Management Service (KMS)?
AWS KMS is a managed service that enables you to easily create and control the keys used for cryptographic operations. The service provides a highly available key generation, storage, management, and auditing solution for you to encrypt or digitally sign data within your own applications or control the encryption of data across AWS services.
Q: Why should I use AWS KMS?
If you are responsible for securing your data across AWS services, you should use it to centrally manage the encryption keys that control access to your data. If you are a developer who needs to encrypt data in your applications, you should use the AWS Encryption SDK with AWS KMS to easily generate, use and protect symmetric encryption keys in your code. If you are a developer who needs to digitally sign or verify data using asymmetric keys, you should use the service to create and manage the private keys you’ll need. If you’re looking for a scalable key management infrastructure to support your developers and their growing number of applications, you should use it to reduce your licensing costs and operational burden. If you’re responsible for proving data security for regulatory or compliance purposes, you should use it because it facilitates proving your data is consistently protected. It’s also in scope for a broad set of industry and regional compliance regimes.
Q: How do I get started with AWS KMS?
The easiest way is to get started using the service is to choose to encrypt your data within supported AWS services using AWS managed master keys that are automatically created in your account for each service. If you want full control over the management of your keys, including the ability to share access to keys across accounts or services, you can create your own customer master keys (CMKs) in AWS KMS. You can also use the CMKs that you create directly within your own applications. AWS KMS can be accessed from the KMS console that is grouped under Security, Identity and Compliance on the AWS Services home page of the AWS Console. AWS KMS APIs can also be accessed directly through the AWS KMS Command Line Interface or AWS SDK for programmatic access. AWS KMS APIs can also be used indirectly to encrypt data within your own applications by using the AWS Encryption SDK. Visit the Getting Started page to learn more.
Q: In what Regions is AWS KMS available?
Availability is listed on our global Products and Services by Region page.
Asymmetric keys are currently only available in Northern Virginia, Oregon, Sydney, Ireland, and Tokyo.
Q: What key management features are available in AWS KMS?
You can perform the following key management functions:
- Create symmetric and asymmetric keys where the key material is only ever used within the service
- Create symmetric keys where the key material is generated and used within a custom key store under your control*
- Import your own symmetric key material for use within the service
- Create both symmetric and asymmetric data key pairs for local use within your applications
- Define which IAM users and roles can manage keys
- Define which IAM users and roles can use keys to encrypt and decrypt data
- Choose to have keys that were generated by the service to be automatically rotated on an annual basis
- Temporarily disable keys so they cannot be used by anyone
- Re-enable disabled keys
- Schedule the deletion of keys that you no longer use
- Audit use of keys by inspecting logs in AWS CloudTrail
* The use of custom key stores requires CloudHSM resources to be available in your account.
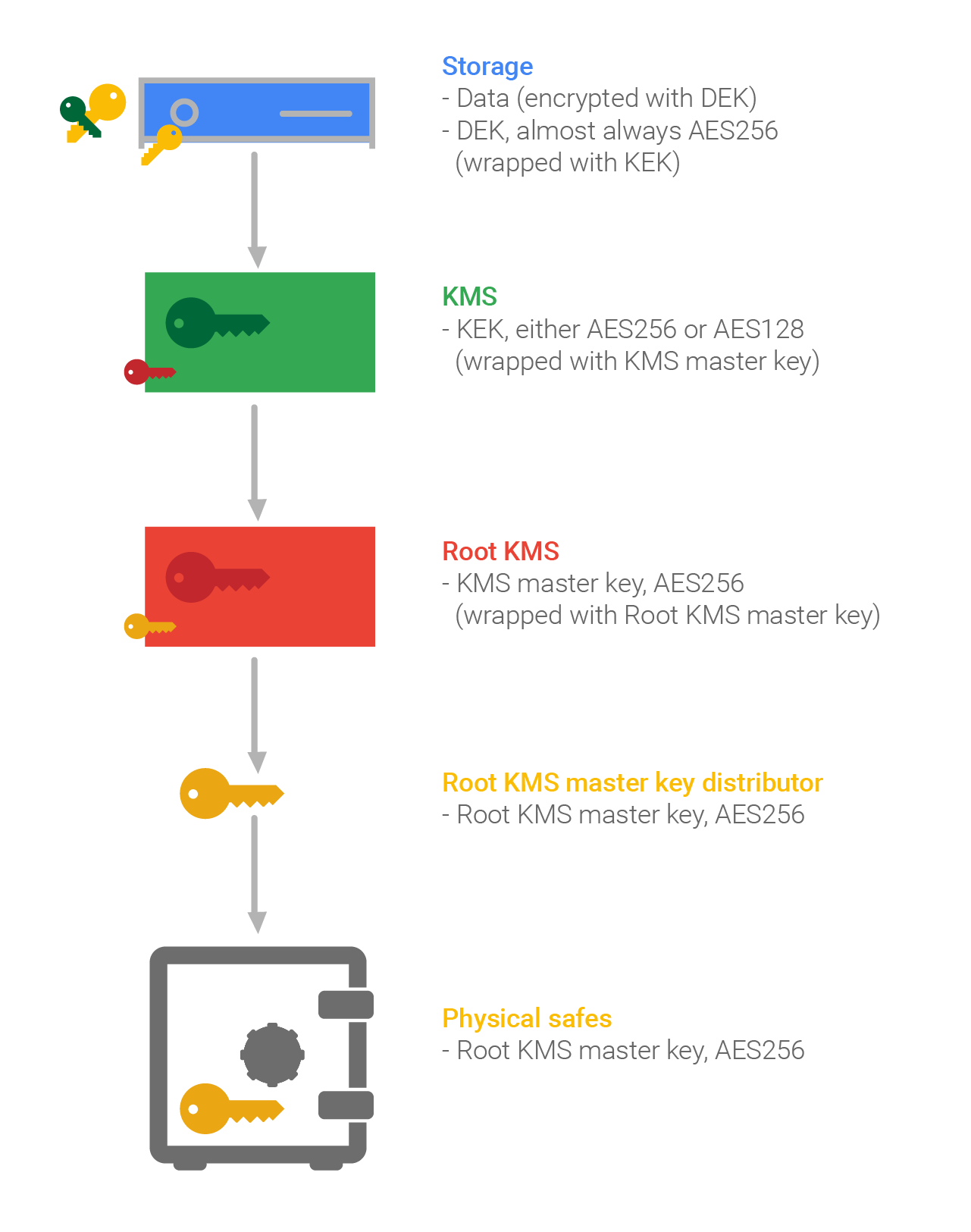
AWS services and client-side toolkits that integrate with AWS KMS use a method known as envelope encryption to protect your data. Under this method, AWS KMS generates data keys which are used to encrypt data locally in the AWS service or your application. The data keys are themselves encrypted under a CMK you define. Data keys are not retained or managed by AWS KMS. AWS services encrypt your data and store an encrypted copy of the data key along with the encrypted data. When a service needs to decrypt your data, it requests AWS KMS to decrypt the data key using your CMK. If the user requesting data from the AWS service is authorized to decrypt under your CMK, the AWS service will receive the decrypted data key from AWS KMS. The AWS service then decrypts your data and returns it in plaintext. All requests to use your CMKs are logged in AWS CloudTrail so you can understand who used which key under what context and when they used it.

Q: Where is my data encrypted if I use AWS KMS?
There are typically three scenarios for how data is encrypted using AWS KMS. Firstly, you can use AWS KMS APIs directly to encrypt and decrypt data using your CMKs stored in the service. Secondly, you can choose to have AWS services encrypt your data using your CMKs stored in the service. In this case data is encrypted using data keys that are protected by your CMKs. Thirdly, you can use the AWS Encryption SDK that is integrated with AWS KMS to perform encryption within your own applications, whether they operate in AWS or not.
Q: Why use envelope encryption? Why not just send data to AWS KMS to encrypt directly?
While AWS KMS does support sending data up to 4 KB to be encrypted directly, envelope encryption can offer significant performance benefits. When you encrypt data directly with AWS KMS it must be transferred over the network. Envelope encryption reduces the network load since only the request and delivery of the much smaller data key go over the network. The data key is used locally in your application or encrypting AWS service, avoiding the need to send the entire block of data to AWS KMS and suffer network latency.
Q: What’s the difference between a CMK I create and CMKs created automatically for me by other AWS services?
You have the option of selecting a specific CMK to use when you want an AWS service to encrypt data on your behalf. These are known as customer managed CMKs and you have full control over them. You define the access control and usage policy for each key and you can grant permissions to other accounts and services to use them. If you don’t specify a CMK, the service in question will create an AWS managed CMK the first time you try to create an encrypted resource within that service. AWS will manage the policies associated with AWS managed CMKs on your behalf. You can track AWS managed keys in your account and all usage is logged in AWS CloudTrail, but you have no direct control over the keys themselves.
Q: Why should I create my own customer master keys?
Creating your own CMK gives you more control than you have with AWS managed CMKs. When you create a symmetric customer managed CMK, you can choose to use key material generated by AWS KMS, generated within an AWS CloudHSM cluster (custom key store), or import your own key material. You can define an alias and description for the key and opt-in to have the key automatically rotated once per year if it was generated by AWS KMS. You also define all the permissions on the key to control who can use or manage the key. With asymmetric customer managed CMKs, there are a couple of caveats to management: the key material can only be generated within AWS KMS HSMs and there is no option for automatic key rotation.
Q: Can I bring my own keys to AWS KMS?
Yes. You can import a copy of your key from your own key management infrastructure to AWS KMS and use it with any integrated AWS service or from within your own applications. You cannot import asymmetric CMKs into AWS KMS.
Q: When would I use an imported key?
You can use an imported key to get greater control over the creation, lifecycle management, and durability of your key in AWS KMS. Imported keys are designed to help you meet your compliance requirements which may include the ability to generate or maintain a secure copy of the key in your infrastructure, and the ability to immediately delete the imported copy of the key from AWS infrastructure.
Q: What type of keys can I import?
You can import 256-bit symmetric keys.
Q: How is the key that I import into AWS KMS protected in transit?
During the import process, your key must be wrapped by an AWS KMS-provided public key using one of two RSA PKCS#1 schemes. This ensures that your encrypted key can only be decrypted by AWS KMS.
Q: What’s the difference between a key I import and a key I generate in AWS KMS?
There are two main differences:
- You are responsible for maintaining a copy of your imported keys in your key management infrastructure so that you can re-import them at any time. AWS, however, ensures the availability, security, and durability of keys generated by AWS KMS on your behalf until you schedule the keys for deletion.
- You may set an expiration period for an imported key. AWS KMS will automatically delete the key material after the expiration period. You may also delete imported key material on demand. In both cases the key material itself is deleted but the CMK reference in AWS KMS and associated metadata are retained so that the key material can be re-imported in the future. Keys generated by AWS KMS do not have an expiration time and cannot be deleted immediately; there is a mandatory 7 to 30 day wait period. All customer managed CMKs, irrespective of whether the key material was imported, can be manually disabled or scheduled for deletion. In this case the CMK itself is deleted, not just the underlying key material.
Q: Can I rotate my keys?
Yes. You can choose to have AWS KMS automatically rotate CMKs every year, provided that those keys were generated within AWS KMS HSMs. Automatic key rotation is not supported for imported keys, asymmetric keys, or keys generated in an AWS CloudHSM cluster using the AWS KMS custom key store feature. If you choose to import keys to AWS KMS or asymmetric keys or use a custom key store, you can manually rotate them by creating a new CMK and mapping an existing key alias from the old CMK to the new CMK.
Q: Do I have to re-encrypt my data after keys in AWS KMS are rotated?
If you choose to have AWS KMS automatically rotate keys, you don’t have to re-encrypt your data. AWS KMS automatically keeps previous versions of keys to use for decryption of data encrypted under an old version of a key. All new encryption requests against a key in AWS KMS are encrypted under the newest version of the key.
If you manually rotate your imported or custom key store keys, you may have to re-encrypt your data depending on whether you decide to keep old versions of keys available.
Q: Can I delete a key from AWS KMS?
Yes. You can schedule a customer master key and associated metadata that you created in AWS KMS for deletion, with a configurable waiting period from 7 to 30 days. This waiting period allows you to verify the impact of deleting a key on your applications and users that depend on it. The default waiting period is 30 days. You can cancel key deletion during the waiting period. The key cannot be used if it is scheduled for deletion until you cancel the deletion during the waiting period. The key gets deleted at the end of the configurable waiting period if you don’t cancel the deletion. Once a key is deleted, you can no longer use it. All data protected under a deleted master key is inaccessible.
For customer master keys with imported key material, you can delete the key material without deleting the customer master key id or metadata in two ways. First, you can delete your imported key material on demand without a waiting period. Second, at the time of importing the key material into the customer master key, you may define an expiration time for how long AWS can use your imported key material before it is deleted. You can re-import your key material into the customer master key if you need to use it again.
Generate Data Key From Kms Free
Q: What should I do if my imported key material has expired or I accidentally deleted it?
You can re-import your copy of the key material with a valid expiration period to AWS KMS under the original customer master key so it can be used.
Q: Can I be alerted that I need to re-import the key?
Yes. Once you import your key to a customer master key, you will receive an Amazon CloudWatch Metric every few minutes that counts down the time to expiration of the imported key. You will also receive an Amazon CloudWatch Event once the imported key under your customer master key expires. You can build logic that acts on these metrics or events and automatically re-imports the key with a new expiration period to avoid an availability risk.
Q: Can I use AWS KMS to help manage encryption of data outside of AWS cloud services?
Yes. AWS KMS is supported in AWS SDKs, AWS Encryption SDK, the Amazon DynamoDB Client-side Encryption, and the Amazon S3 Encryption Client to facilitate encryption of data within your own applications wherever they run. Visit the AWS Crypto Tools and Developing on AWS website for more information.
Q: Is there a limit to the number of keys I can create in AWS KMS?
You can create up to 10000 CMKs per account per region. As both enabled and disabled CMKs count towards the limit, we recommend deleting disabled keys that you no longer use. AWS managed CMKs created on your behalf for use within supported AWS services do not count against this limit. There is no limit to the number of data keys that can be derived using a CMK and used in your application or by AWS services to encrypt data on your behalf. You may request a limit increase for CMKs by visiting the AWS Support Center.
Q: What types of symmetric key types and algorithms are supported?
AWS KMS supports 256-bit keys when creating a CMK. Generated data keys returned to the caller can be 256-bit, 128-bit, or an arbitrary value up to 1024-bits. When AWS KMS uses a 256-bit CMK on your behalf, the AES algorithm in Galois Counter Mode (AES-GCM) is used.
Q: What kind of asymmetric key types are supported?
AWS KMS supports the following asymmetric key types - RSA 2048, RSA 3072, RSA 4096, ECC NIST P-256, ECC NIST P-384, ECC NIST-521, and ECC SECG P-256k1.
Q: What kinds of asymmetric encryption algorithms are supported?
AWS KMS supports the RSAES_OAEP_SHA_1 and RSAES_OAEP_SHA_256 encryption algorithms with RSA 2048, RSA 3072, and RSA 4096 key types. Encryption algorithms cannot be used with the elliptic curve key types (ECC NIST P-256, ECC NIST P-384, ECC NIST-521, and ECC SECG P-256k1).
Q: What kinds of asymmetric signing algorithms are supported?
When using RSA key types, AWS KMS supports the RSASSA_PSS_SHA_256, RSASSA_PSS_SHA_384, RSASSA_PSS_SHA_512, RSASSA_PKCS1_V1_5_SHA_256, RSASSA_PKCS1_V1_5_SHA_384, and RSASSA_PKCS1_V1_5_SHA_512 signing algorithms.
When using elliptic curve key types, AWS KMS supports the ECDSA_SHA_256, ECDSA_SHA_384, and ECDSA_SHA_512 signing algorithms.
Q: Can symmetric CMKs be exported out of the service in plain text?
No. A symmetric CMK or the private portion of an asymmetric CMK cannot be exported in plain text from the HSMs. The public portion of an asymmetric CMK can be exported from the console or by calling the “GetPublicKey” API.
Q: Can data keys and data key pairs be exported out of the HSMs in plain text?
Yes. The symmetric data keys can be exported using either the “GenerateDataKey” API or the “GenerateDataKeyWithoutPlaintext” API. And the private and public portion of asymmetric data key pairs can both be exported out of AWS KMS using either the “GenerateDataKeyPair” API or the “GenerateDataKeypairWithoutPlaintext” API.
Q: How are data keys and data key pairs protected for storage outside the service?
The symmetric data key or the private portion of the asymmetric data key is encrypted under the symmetric CMK you define when you request AWS KMS to generate the data key.
Q: How do I use the public portion of an asymmetric CMK?
The public portion of the asymmetric key material is generated in AWS KMS and can be used for digital signature verification by calling the “Verify” API, or for public key encryption by calling the “Encrypt” API. The public key can also be used outside of AWS KMS for verification or encryption. You can call the GetPublicKey API to retrieve the public portion of the asymmetric CMK.
Q: What is the size limit for data sent to AWS KMS for asymmetric operations?
The size limit is 4KB. If you want to digitally sign data larger than 4KB, you have the option to create a message digest of the data and send it to AWS KMS. The digital signature is created over the digest of the data and returned. You specify whether you are sending the full message or a message digest as a parameter in the Sign API request. Any data submitted to the Encrypt, Decrypt, or Re-Encrypt APIs that require use of asymmetric operations must also be less than 4KB.
Q: How can I distinguish between asymmetric or symmetric CMKs I have created?
In the console, each key will have a new field called “Key Type”. It will have either the value “Asymmetric Key” or “Symmetric Key” to indicate the type of key. The “DescribeKey” API will return a “KeyUsage” field that will specify if the key can be used to sign or encrypt.
Q: Is automatic rotation of asymmetric CMKs supported?
No. Automatic key rotation is not supported for asymmetric CMKs. You can manually rotate them by creating a new CMK and mapping an existing key alias from the old CMK to the new CMK.
Q: Can a single asymmetric CMK be used for both encryption and signing?
No. When creating a CMK, you must specify whether the key can be used for decrypt or sign operations. An RSA key type can be used for signing or encryption operations, but not both. Elliptic curve key types can only be used for signing operations.
Q: Are there service limits related to asymmetric keys?
Yes. The request per second rate limits are different for different key types and algorithms. Please refer to the AWS KMS limits page for details.
Q: Do asymmetric keys work with AWS KMS custom key stores or the Import Key feature?
No. You cannot use the custom key store functionality with asymmetric keys nor can you import asymmetric keys into AWS KMS.
Q: Can I use asymmetric CMKs for digital signing applications that require digital certificates?
Not directly. AWS KMS doesn’t store or associate digital certificates with asymmetric CMKs it creates. You could choose to have a certificate authority such as ACM PCA issue a certificate for the public portion of your asymmetric CMK. This will allow the entities that are consuming your public key to verify that the public key indeed belongs to you.
Q: For what use scenarios should I use ACM Private Certificate Authority vs. AWS KMS?
The primary reason to use the ACM Private Certificate Authority (CA) service is to provide a public key infrastructure (PKI) for the purpose of identifying entities and securing network connections. PKI provides processes and mechanisms, primarily using X.509 certificates, to put structure around public key cryptographic operations. Certificates provide an association between an identity and a public key. The certification process in which a certificate authority issues a certificate allows the trusted certificate authority to assert the identity of another entity by signing a certificate. PKI provides identity, distributed trust, key lifecycle management, and certificate status vended through revocation. These functions add important processes and infrastructure to the underlying asymmetric cryptographic keys and algorithms provided by AWS KMS.
ACM Private CA allows you to issue certificates to identify web and application servers, service meshes, VPN users, internal API endpoints, and IoT devices. Certificates let you establish the identity of these resources and create encrypted TLS/SSL communications channels. If you are considering using asymmetric keys for TLS termination on web or application servers, Elastic Load Balancers, API Gateway endpoints, EC2 instances or containers, you should consider using ACM Private CA for issuing certificates and providing a PKI infrastructure.
In contrast, AWS KMS lets you generate, manage, and use asymmetric keys for digital signing and/or encryption operations that don’t require certificates. While certificates can enable verification of sender and recipient identity between untrusted parties, the kind of raw asymmetric operations offered by AWS KMS are typically useful when you have other mechanisms to prove identity or don’t need to prove it at all to get the security benefit you desire.
Q: Can I use my applications’ cryptographic API providers such as OpenSSL, JCE, Bouncy Castle, or CNG with AWS KMS?
There is no native integration offered by AWS KMS for any other cryptographic API providers. You must use AWS KMS APIs directly or through the AWS SDK to integrate signing and encryption capabilities into your applications.
Q: Does AWS KMS offer a Service Level Agreement (SLA)?
Yes. The AWS KMS SLA provides for a service credit if a customer's monthly uptime percentage is below our service commitment in any billing cycle.
[ aws . kms ]
Description¶
Generates a unique symmetric data key. This operation returns a plaintext copy of the data key and a copy that is encrypted under a customer master key (CMK) that you specify. You can use the plaintext key to encrypt your data outside of AWS KMS and store the encrypted data key with the encrypted data.
To generate a data key, specify the symmetric CMK that will be used to encrypt the data key. You cannot use an asymmetric CMK to generate data keys. To get the type of your CMK, use the DescribeKey operation.
You must also specify the length of the data key. Use either the KeySpec or NumberOfBytes parameters (but not both). For 128-bit and 256-bit data keys, use the KeySpec parameter.
If the operation succeeds, the plaintext copy of the data key is in the Plaintext field of the response, and the encrypted copy of the data key in the CiphertextBlob field.
To get only an encrypted copy of the data key, use GenerateDataKeyWithoutPlaintext . To generate an asymmetric data key pair, use the GenerateDataKeyPair or GenerateDataKeyPairWithoutPlaintext operation. To get a cryptographically secure random byte string, use GenerateRandom .
You can use the optional encryption context to add additional security to the encryption operation. If you specify an EncryptionContext , you must specify the same encryption context (a case-sensitive exact match) when decrypting the encrypted data key. Otherwise, the request to decrypt fails with an InvalidCiphertextException. For more information, see Encryption Context in the AWS Key Management Service Developer Guide .
The CMK that you use for this operation must be in a compatible key state. For details, see How Key State Affects Use of a Customer Master Key in the AWS Key Management Service Developer Guide .
We recommend that you use the following pattern to encrypt data locally in your application:
- Use the GenerateDataKey operation to get a data encryption key.
- Use the plaintext data key (returned in the Plaintext field of the response) to encrypt data locally, then erase the plaintext data key from memory.
- Store the encrypted data key (returned in the CiphertextBlob field of the response) alongside the locally encrypted data.
To decrypt data locally:
- Use the Decrypt operation to decrypt the encrypted data key. The operation returns a plaintext copy of the data key.
- Use the plaintext data key to decrypt data locally, then erase the plaintext data key from memory.
See also: AWS API Documentation
See 'aws help' for descriptions of global parameters.
Synopsis¶
Options¶
--key-id (string)
Identifies the symmetric CMK that encrypts the data key.
To specify a CMK, use its key ID, Amazon Resource Name (ARN), alias name, or alias ARN. When using an alias name, prefix it with 'alias/' . To specify a CMK in a different AWS account, you must use the key ARN or alias ARN.
For example:
- Key ID: 1234abcd-12ab-34cd-56ef-1234567890ab
- Key ARN: arn:aws:kms:us-east-2:111122223333:key/1234abcd-12ab-34cd-56ef-1234567890ab
- Alias name: alias/ExampleAlias
- Alias ARN: arn:aws:kms:us-east-2:111122223333:alias/ExampleAlias
To get the key ID and key ARN for a CMK, use ListKeys or DescribeKey . To get the alias name and alias ARN, use ListAliases .
--encryption-context (map)
Specifies the encryption context that will be used when encrypting the data key.
An encryption context is a collection of non-secret key-value pairs that represents additional authenticated data. When you use an encryption context to encrypt data, you must specify the same (an exact case-sensitive match) encryption context to decrypt the data. An encryption context is optional when encrypting with a symmetric CMK, but it is highly recommended.
For more information, see Encryption Context in the AWS Key Management Service Developer Guide .
Shorthand Syntax:
JSON Syntax:
--number-of-bytes (integer)
Specifies the length of the data key in bytes. For example, use the value 64 to generate a 512-bit data key (64 bytes is 512 bits). For 128-bit (16-byte) and 256-bit (32-byte) data keys, use the KeySpec parameter.
You must specify either the KeySpec or the NumberOfBytes parameter (but not both) in every GenerateDataKey request.
--key-spec (string)
Specifies the length of the data key. Use AES_128 to generate a 128-bit symmetric key, or AES_256 to generate a 256-bit symmetric key.
You must specify either the KeySpec or the NumberOfBytes parameter (but not both) in every GenerateDataKey request.
Possible values:
- AES_256
- AES_128
--grant-tokens (list)
A list of grant tokens.
For more information, see Grant Tokens in the AWS Key Management Service Developer Guide .
Syntax:
--cli-input-json (string)Performs service operation based on the JSON string provided. The JSON string follows the format provided by --generate-cli-skeleton. If other arguments are provided on the command line, the CLI values will override the JSON-provided values. It is not possible to pass arbitrary binary values using a JSON-provided value as the string will be taken literally.
--generate-cli-skeleton (string)Prints a JSON skeleton to standard output without sending an API request. If provided with no value or the value input, prints a sample input JSON that can be used as an argument for --cli-input-json. If provided with the value output, it validates the command inputs and returns a sample output JSON for that command.
See 'aws help' for descriptions of global parameters.
Output¶
Generate Data Key From Kms Pdf
CiphertextBlob -> (blob)
Plaintext -> (blob)
Data Key Entry
Generate Data Key From Kms To Meters
KeyId -> (string)